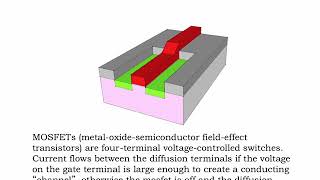
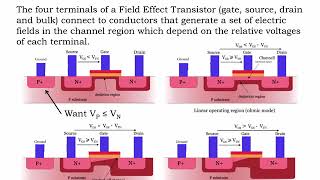
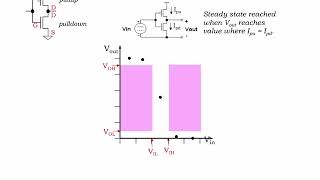
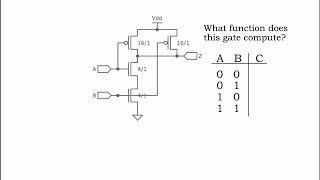
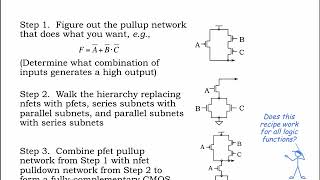
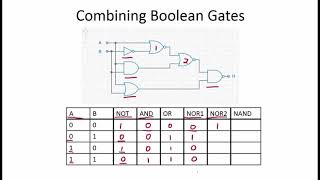
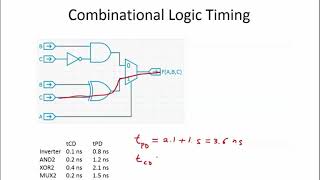
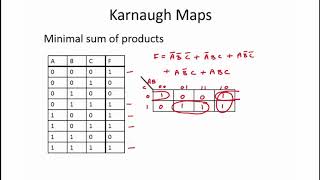
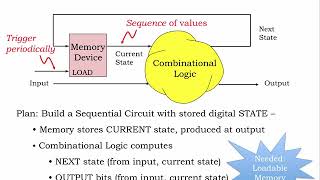
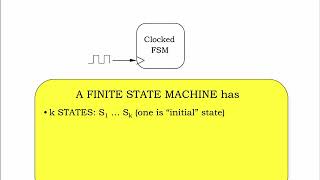
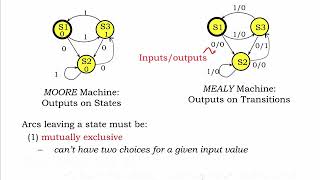
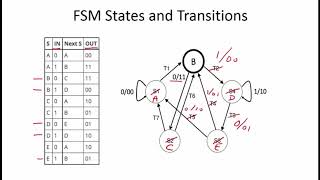
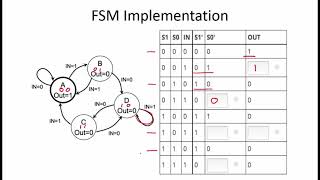
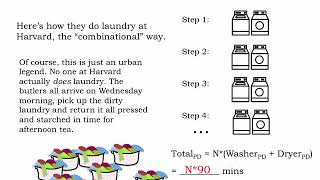
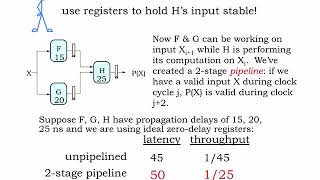
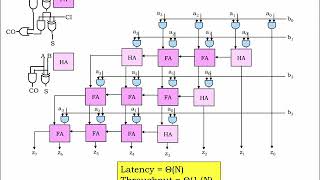
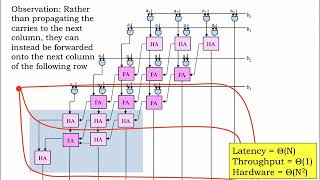
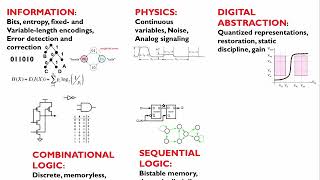
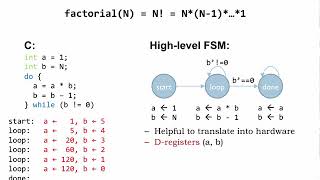
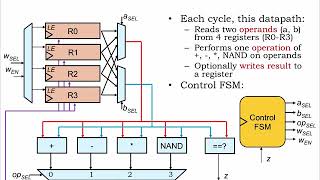
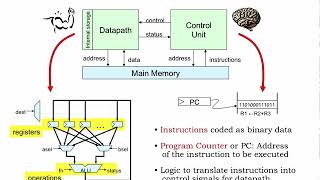
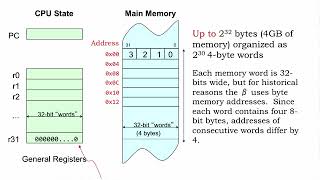
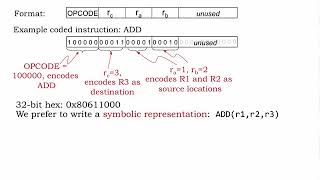
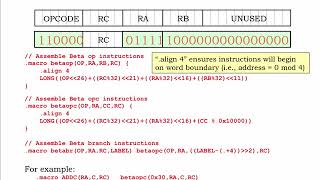
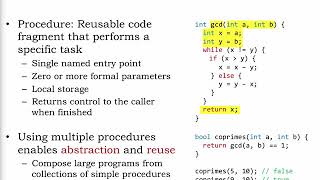
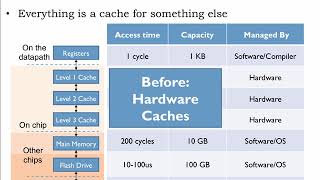
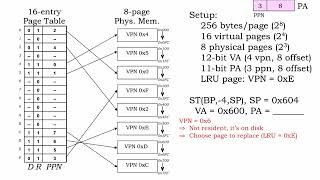
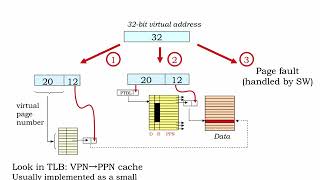
6.004 offers an introduction to the engineering of digital systems. Starting with MOS transistors, the course develops a series of building blocks — logic gates, combinational and sequential circuits, finite-state machines, computers and finally complete systems. Both hardware and software mechanisms are explored through a series of design examples.
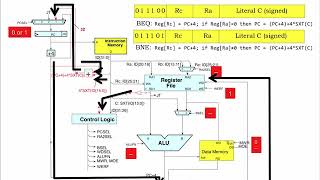
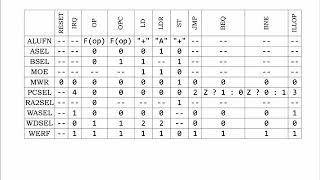
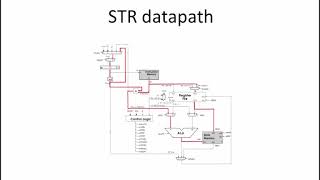
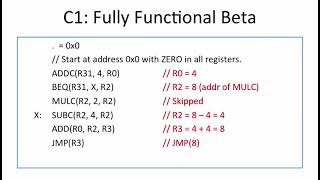
6.004 is required material for any EECS undergraduate who wants to understand (and ultimately design) digital systems. A good grasp of the material is essential for later courses in digital design, computer architecture and systems. The problem sets and lab exercises are intended to give students “hands-on” experience in designing digital systems; each student completes a gate-level design for a reduced instruction set computer (RISC) processor during the semester.
| 來源 | MIT 開放式課程 |
| 科系 | Electrical Engineering and Computer Science |
| 語言 | English |
| 影片數 | 172 |